Security
- Home /
- Categories /
- Security
Stop Debating When Quantum Breaks RSA. Start Building the Ability to Switch.
Another week, another quantum breakthrough. On March 2, the Advanced Quantum Technologies Institute announced the JVG algorithm, a hybrid classical-quantum approach that, they claim, could factor RSA keys with fewer than 5,000 qubits. That is three orders of magnitude below the million-qubit estimates we have been working with for years.
Read More
AWS Config Just Added 30 Resource Types. The Bedrock AgentCore Ones Matter Most.
AWS quietly announced support for 30 new resource types in AWS Config on March 2, 2026. If you’re the kind of person who skims these announcements and moves on, I get it. Most Config resource type expansions are incremental. This one isn’t.
Read More
LLM Prompt Injection Attacks: Types, Examples & Mitigation Strategies
If you’ve been building with LLMs lately, you’re probably as excited as I am about the possibilities! But let me tell you about something that’s been keeping security folks up at night… prompt injection vulnerabilities.
Read More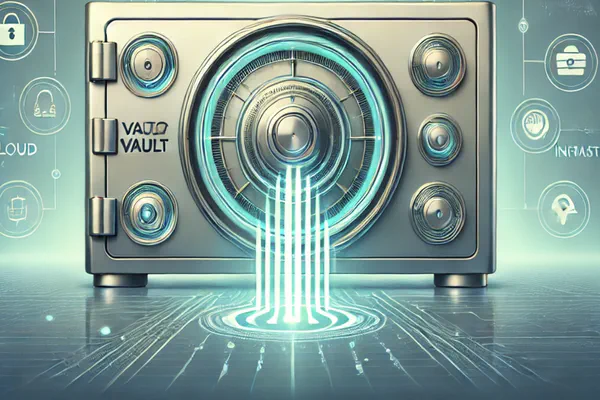
HashiCorp Vault Auto Unseal Guide: AWS KMS, Transit & Configuration
Unsealing Vault after a server restart is one of those tasks that, while essential, can quickly become cumbersome—especially when you’re managing multiple Vault nodes or clusters. Enter Auto Unseal, a lifesaver in production environments, as it automates the process of securely unsealing Vault without requiring manual intervention.
Read More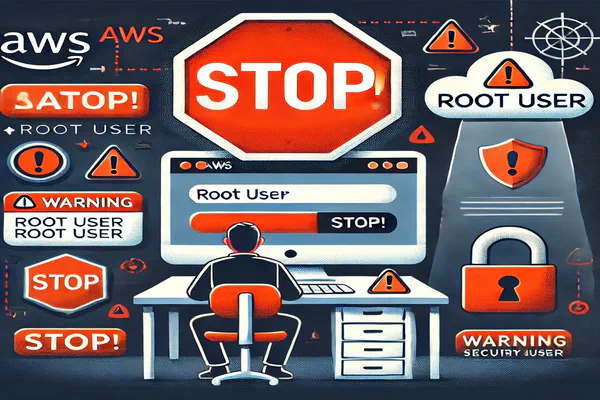
AWS Root User Security: Best Practices for IAM & Root Account Lockdown
Hey there, tech enthusiasts! Ever felt that little thrill of power when you get root access on a system? It’s like holding the keys to the kingdom, right?
Read More
A Reminder of the Power of AWS Config
Today, I was reminded of the rich content stored in AWS Config and how easily it can reveal so much about an AWS Organisation across one or many accounts.
Read More
HashiCorp Vault Production Hardening Guide: Security Best Practices (2026)
So, you’ve got Vault up and running, and you’re feeling pretty good about storing and managing secrets. But here’s the thing—running Vault in production is a whole different game. It’s not just about turning it on; it’s about hardening it to ensure that your Vault instance is secure, reliable, and resilient against attacks.
Read More
HashiCorp Vault Secrets Management: Best Practices, Rotation & Dynamic Secrets
What is HashiCorp Vault? HashiCorp Vault is a secrets management platform that centralises how your organisation stores, accesses, and distributes sensitive data — API keys, database credentials, certificates, encryption keys, and more. Rather than scattering secrets across config files, environment variables, and shared spreadsheets, Vault gives you a single source of truth with fine-grained access control, automatic rotation, and a full audit trail.
Read More
Security Hub now supports Custom AWS Config Rules
AWS recently announced an integration that I’m a little excited about!
Read More