Sovereign Cloud Gets Real When Security Services Show Up
- Stephen Jones
- Aws
- April 1, 2026
Table of Contents
In March 2026, AWS Network Firewall became available in the European Sovereign Cloud. If you’re not paying close attention to the sovereign cloud space, that probably sounds like a minor service addition. I’d argue it’s one of the most significant milestones since the partition launched.
Here’s my take: sovereign cloud becomes credible when security services arrive — not just compute, storage, and marketing slides. After advising regulated clients through this exact evaluation, I keep coming back to one metric that matters more than region launches.
With Network Firewall now sitting alongside GuardDuty and Security Hub, AWS has assembled what I’d call the foundation of a security stack for regulated workloads.
Why Security Service Parity Is the Metric That Matters
When AWS launched the European Sovereign Cloud on January 15, 2026, in Brandenburg, Germany, the headlines focused on the 7.8 billion euro investment over 15 years, the separate European corporate entity, and the commitment to operation exclusively by EU residents. All of that matters. But it’s table stakes.
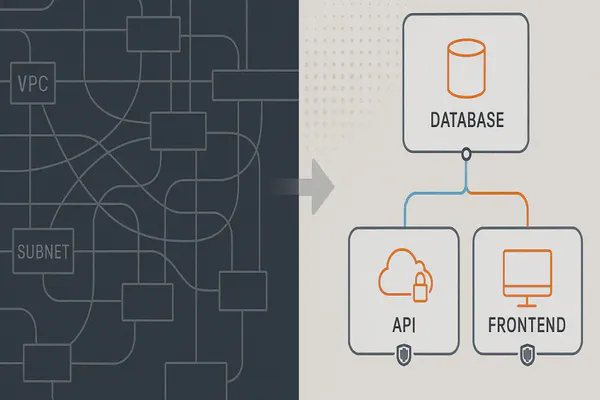
What actually determines whether enterprises can deploy production workloads is the service catalogue. Right now, approximately 90 of the 240+ AWS services are available — roughly 37% parity. That number tells you the European Sovereign Cloud is still in its early chapters.
But not all services carry equal weight. Compute and storage get you a sandbox. Databases get you development environments. Security services get you production readiness. That’s the hierarchy, and it’s the one most sovereign cloud marketing conveniently ignores.
Network Firewall matters because regulated industries — financial services, healthcare, government, critical infrastructure — cannot deploy workloads without managed stateful firewall inspection. (I covered the Australian sovereignty angle with Bedrock earlier — the same “show me the services, not the press release” logic applies globally.) It’s not a nice-to-have. It’s a compliance prerequisite — particularly as DORA operational resilience requirements take effect across European financial services.
The Gaps That Still Matter
- No WAF. No web application firewall protection for public-facing applications.
- No CloudFront or Shield. No managed CDN and no managed DDoS protection.
- No IAM Identity Center. No centralised identity management.
- No CodePipeline or CodeBuild. Your CI/CD pipeline either lives outside the sovereign boundary or you’re self-managing.
- Single-region only. No second region for disaster recovery.
The Competitive Landscape: Three Different Bets
Azure leads on maturity. Microsoft completed its EU Data Boundary in 2024, offering a broad service catalogue with data residency guarantees. The approach is primarily a policy boundary layered on existing global infrastructure — pragmatic and working today, but less architecturally absolute.
AWS leads on architectural ambition. The European Sovereign Cloud is a fully separate partition — distinct infrastructure, separate corporate entity, EU-resident operations. It’s the harder path, which explains the smaller catalogue, but arguably the stronger long-term sovereignty story.
European-native providers lead on sovereignty purity. OVHcloud with SecNumCloud certification and STACKIT (backed by the Schwarz Group) offer what hyperscalers structurally cannot: European ownership top to bottom. The trade-off is ecosystem breadth.
Three Scenarios: A Decision Framework
European sovereign cloud spending is forecast to triple between 2025 and 2027. I see three paths:
Scenario 1: Early Mover (Q2 2026) — Accept current constraints, build operational expertise. You’ll lean on the foundation of the security stack and third-party tooling where native services don’t exist. Advantage: first-mover learning. Risk: building patterns around a catalogue that will change.
Scenario 2: Wait for Parity (Q4 2026 - Q1 2027) — Need WAF, CloudFront/Shield, IAM Identity Center, or multi-region DR before deploying production workloads. Run proof-of-concept now, move when gaps close. Advantage: more mature platform. Risk: competitors who moved earlier have the operational muscle.
Scenario 3: European-Native (Ongoing) — Sovereignty purity is the primary driver. European ownership and jurisdiction matter more than hyperscaler breadth. Advantage: strongest sovereignty posture. Trade-off: narrower ecosystem.
My Point of View
Most enterprises should be actively running Scenario 2 — planning for the Q4 2026 window — while executing proof-of-concept work now under Scenario 1 conditions. The minimum viable security stack changes the calculus. It’s no longer premature to test real workloads, even if it’s premature to go all-in.
The organisations that treat sovereign cloud as a 2028 problem are going to find themselves scrambling when regulatory pressure accelerates. And the organisations that track security service parity — not region launches, not press releases — will have the clearest picture of actual readiness.
Network Firewall showing up in March 2026 isn’t just a service launch. It’s a signal that the sovereign cloud is graduating from infrastructure to platform. I’ll be watching the service catalogue. You should be too.